Browser extensions turn nearly 1 million browsers into website-scraping bots
Extensions installed on almost 1 million devices have been overriding key security protections to turn browsers into engines that scrape websites on behalf of a paid service, a researcher said.
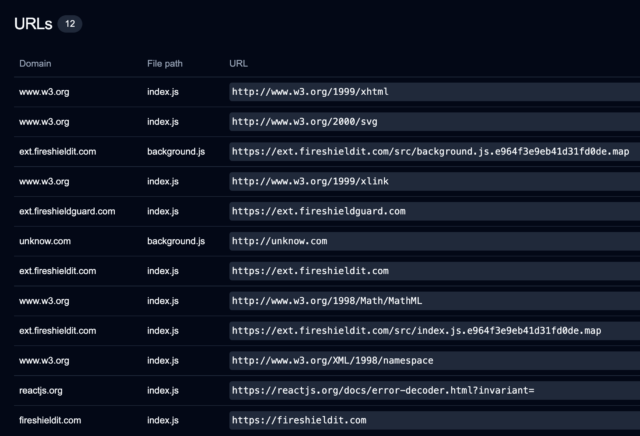
The 245 extensions, available for Chrome, Firefox, and Edge, have racked up nearly 909,000 downloads, John Tuckner of SecurityAnnex reported. The extensions serve a wide range of purposes, including managing bookmarks and clipboards, boosting speaker volumes, and generating random numbers. The common thread among all of them: They incorporate MellowTel-js, an open source JavaScript library that allows developers to monetize their extensions.
Intentional weakening of browsing protections
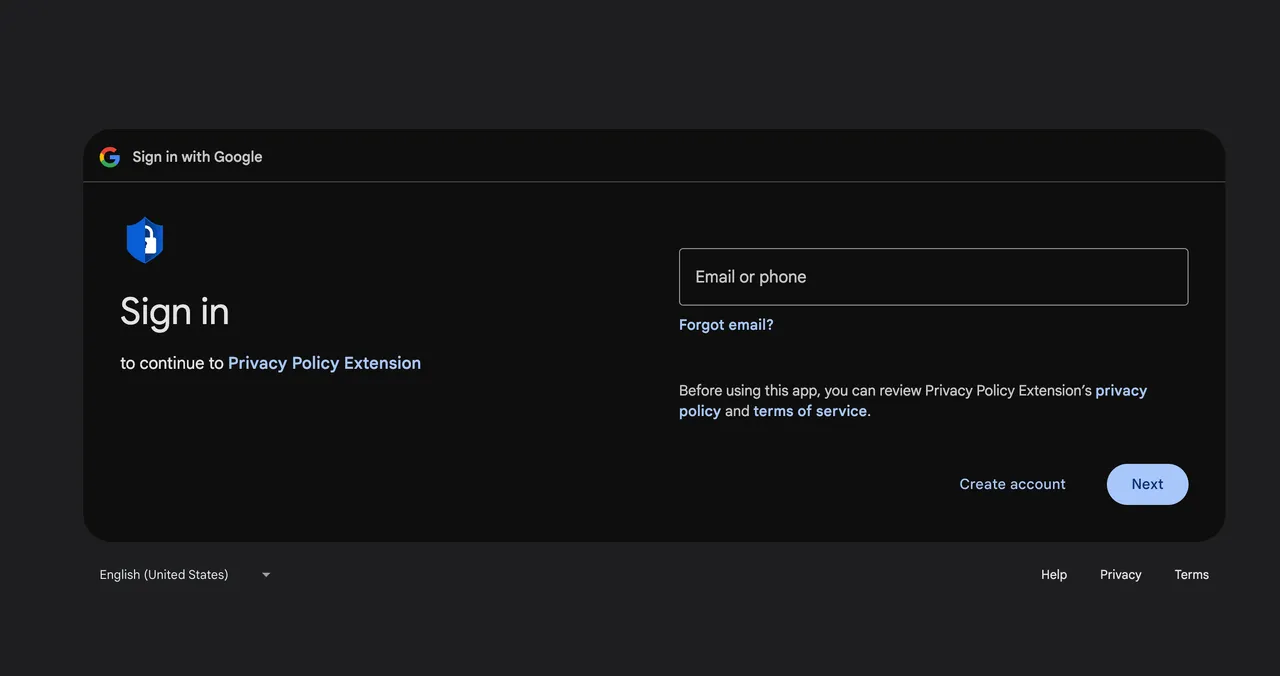
Tuckner and critics say the monetization works by using the browser extensions to scrape websites on behalf of paying customers, which include advertisers. Tuckner reached this conclusion after uncovering close ties between MellowTel and Olostep, a company that bills itself as “the world’s most reliable and cost-effective Web scraping API.” Olostep says its service “avoids all bot detection and can parallelize up to 100K requests in minutes.” Paying customers submit the locations of browsers they want to access specific webpages. Olostep then uses its installed base of extension users to fulfill the request.
“This seems very similar to the scraping instructions we saw while watching the MellowTel library in action,” Tuckner wrote after analyzing the MellowTel code. “I believe we have good reason to think that scraping requests from Olostep are distributed to any of the active extensions which are running the MellowTel library.”
MellowTel’s founder, for his part, has said the purpose of the library is “sharing [users’] bandwidth (without stuffing affiliate links, unrelated ads, or having to collect personal data).” He went on to say that the “primary reason why companies are paying for the traffic is to access publicly available data from websites in a reliable and cost-effective way.” The founder said extension developers receive 55 percent of the revenue, and MellowTel pockets the rest.
Browser extensions turn nearly 1 million browsers into website-scraping bots Read More »