Unicode 16.0 release with new emoji brings character count to 154,998
right there with you, bags-under-eyes emoji —
New designs will roll out to phones, tablets, and PCs over the next few months.

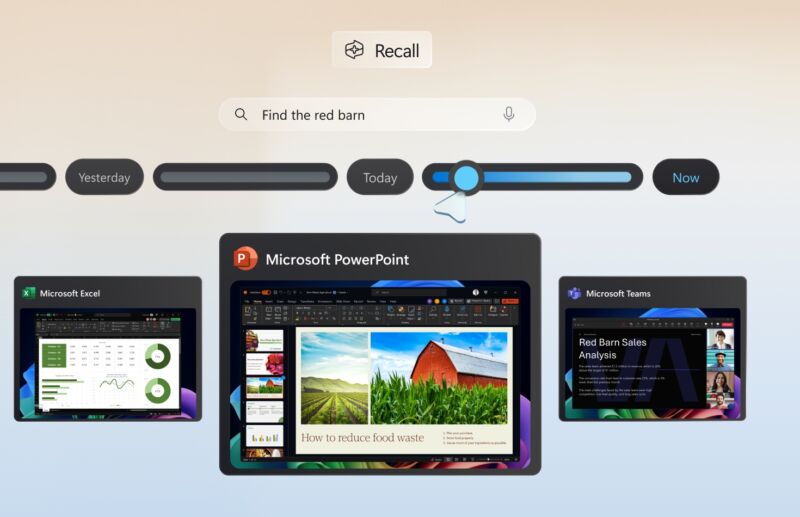
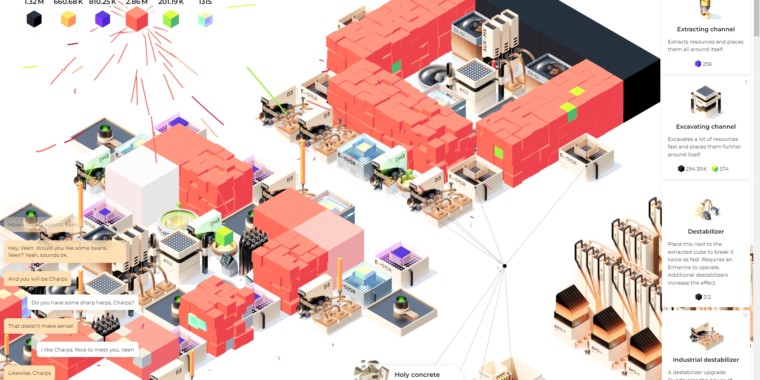
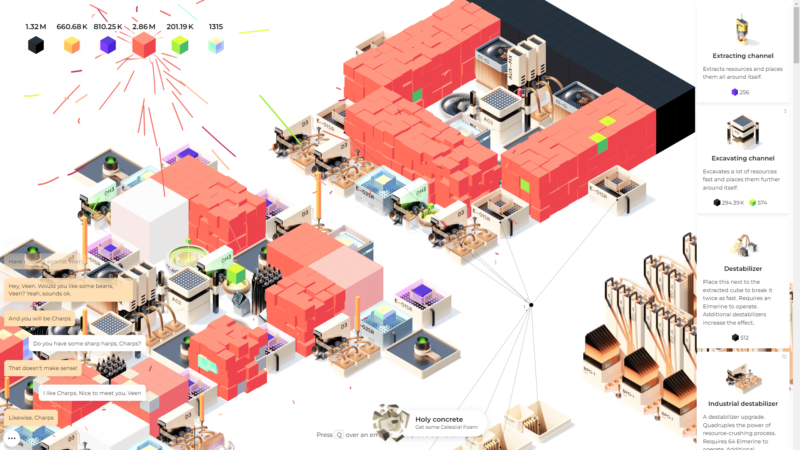
Enlarge / Emojipedia sample images of the new Unicode 16.0 emoji.
The Unicode Consortium has finalized and released version 16.0 of the Unicode standard, the elaborate character set that ensures that our phones, tablets, PCs, and other devices can all communicate and interoperate with each other. The update adds 5,185 new characters to the standard, bringing the total up to a whopping 154,998.
Of those 5,185 characters, the ones that will get the most attention are the eight new emoji characters, including a shovel, a fingerprint, a leafless tree, a radish (formally classified as “root vegetable”), a harp, a purple splat that evokes the ’90s Nickelodeon logo, and a flag for the island of Sark. The standout, of course, is “face with bags under eyes,” whose long-suffering thousand-yard stare perfectly encapsulates the era it has been born into. Per usual, Emojipedia has sample images that give you some idea of what these will look like when they’re implemented by various operating systems, apps, and services.
Unicode 16.0 also adds support for seven new modern and historical scripts: the West African Garay alphabet; the Gurung Khema, Kirat Rai, Ol Onal, and Sunuwar scripts from Northeast India and Nepal; and historical Todhri and Tulu-Tigalari scripts from Albania and Southwest India, respectively.
We last got new emoji in 2023’s Unicode 15.1 update, though all of these designs were technically modifications of existing emoji rather than new characters—many emoji, most notably for skin and hair color variants, use a base emoji plus a modifier emoji, combined together with a “zero-width joiner” (ZWJ) character that makes them display as one character instead. The lime emoji in Unicode 15.1 was actually a lemon emoji combined with the color green; the phoenix was a regular bird joined to the fire emoji. This was likely because 15.1 was only intended as a minor update to 2022’s Unicode 15.0 standard.
Most of the Unicode 16.0 emoji, by contrast, are their own unique characters. The one exception is the Sark flag emoji; flag sequences are created by placing two “regional indicator letters” directly next to each other and don’t require a ZWJ character between them.
Incorporation into the Unicode standard is only the first step that new emoji and other characters take on their journey from someone’s mind to your phone or computer; software makers like Apple, Google, Microsoft, Samsung, and others need to design iterations that fit with their existing spin on the emoji characters, they need to release software updates that use the new characters, and people need to download and install them.
We’ve seen a few people share on social media that the Unicode 16.0 release includes a “greenwashing” emoji designed by Shepard Fairey, an artist best known for the 2008 Barack Obama “Hope” poster. This emoji, and an attempt to gin up controversy around it, is all an elaborate hoax: there’s a fake Unicode website announcing it, a fake lawsuit threat that purports to be from a real natural gas industry group, and a fake Cory Doctorow article about the entire “controversy” published in a fake version of Wired. These were all published to websites with convincing-looking but fake domains, all registered within a couple of weeks of each other in August 2024. The face-with-bags-under-eyes emoji feels like an appropriate response.
Unicode 16.0 release with new emoji brings character count to 154,998 Read More »