Critical takeover vulnerabilities in 92,000 D-Link devices under active exploitation
JUST ADD GET REQUEST —
D-Link won’t be patching vulnerable NAS devices because they’re no longer supported.

Getty Images
Hackers are actively exploiting a pair of recently discovered vulnerabilities to remotely commandeer network-attached storage devices manufactured by D-Link, researchers said Monday.
Roughly 92,000 devices are vulnerable to the remote takeover exploits, which can be remotely transmitted by sending malicious commands through simple HTTP traffic. The vulnerability came to light two weeks ago. The researcher said they were making the threat public because D-Link said it had no plans to patch the vulnerabilities, which are present only in end-of-life devices, meaning they are no longer supported by the manufacturer.
An ideal recipe
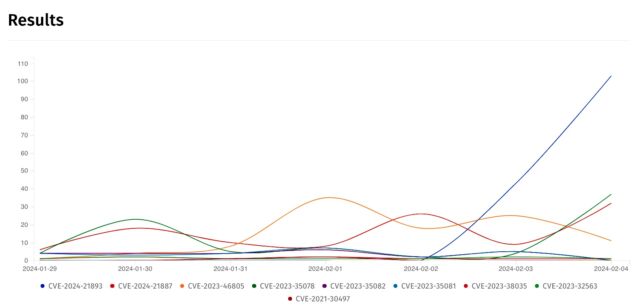
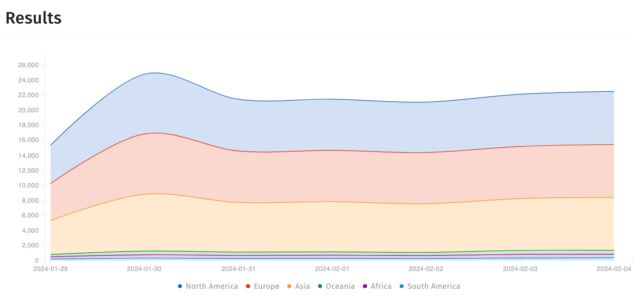
On Monday, researchers said their sensors began detecting active attempts to exploit the vulnerabilities starting over the weekend. Greynoise, one of the organizations reporting the in-the-wild exploitation, said in an email that the activity began around 02: 17 UTC on Sunday. The attacks attempted to download and install one of several pieces of malware on vulnerable devices depending on their specific hardware profile. One such piece of malware is flagged under various names by 40 endpoint protection services.
Security organization Shadowserver has also reported seeing scanning or exploits from multiple IP addresses but didn’t provide additional details.
The vulnerability pair, found in the nas_sharing.cgi programming interface of the vulnerable devices, provide an ideal recipe for remote takeover. The first, tracked as CVE-2024-3272 and carrying a severity rating of 9.8 out of 10, is a backdoor account enabled by credentials hardcoded into the firmware. The second is a command-injection flaw tracked as CVE-2024-3273 and has a severity rating of 7.3. It can be remotely activated with a simple HTTP GET request.
Netsecfish, the researcher who disclosed the vulnerabilities, demonstrated how a hacker could remotely commandeer vulnerable devices by sending a simple set of HTTP requests to them. The code looks like this:
GET /cgi-bin/nas_sharing.cgiuser=messagebus&passwd=&cmd=15&system=In the exploit example below, the text inside the first red rectangle contains the hardcoded credentials—username messagebus and an empty password field—while the next rectangle contains a malicious command string that has been base64 encoded.
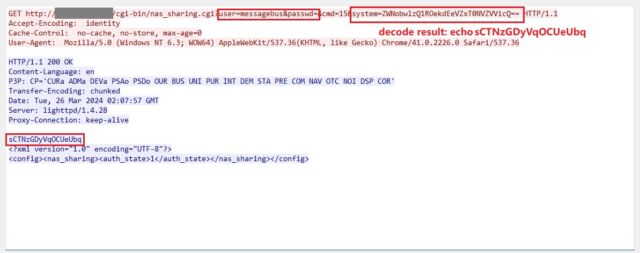
netsecfish
“Successful exploitation of this vulnerability could allow an attacker to execute arbitrary commands on the system, potentially leading to unauthorized access to sensitive information, modification of system configurations, or denial of service conditions,” netsecfish wrote.
Last week, D-Link published an advisory. D-Link confirmed the list of affected devices:
| Model | Region | Hardware Revision | End of Service Life |
Fixed Firmware | Conclusion | Last Updated |
| DNS-320L | All Regions | All H/W Revisions | 05/31/2020 : Link | Not Available | Retire & Replace Device |
04/01/2024 |
| DNS-325 | All Regions | All H/W Revisions | 09/01/2017 : Link | Not Available | Retire & Replace Device | 04/01/2024 |
| DNS-327L | All Regions | All H/W Revisions | 05/31/2020 : Link |
Not Available | Retire & Replace Device | 04/01/2024 |
| DNS-340L | All Regions | All H/W Revisions | 07/31/2019 : Link | Not Available | Retire & Replace Device | 04/01/2024 |
According to netsecfish, Internet scans found roughly 92,000 devices that were vulnerable.
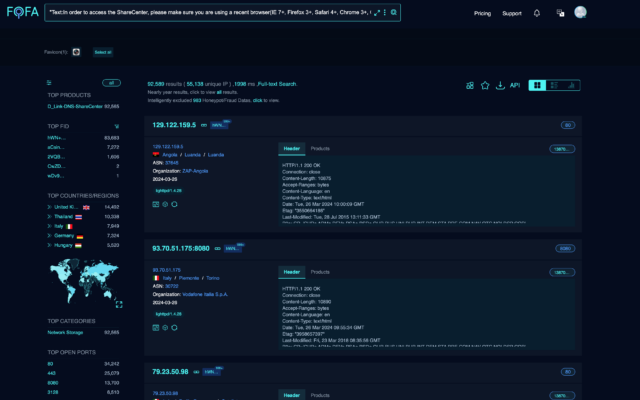
netsecfish
According to the Greynoise email, exploits company researchers are seeing look like this:
GET /cgi-bin/nas_sharing.cgi?dbg=1&cmd=15&user=messagebus&passwd=&cmd=Y2QgL3RtcDsgcLnNo HTTP/1.1Other malware invoked in the exploit attempts include:
- skid.arm – https://www.virustotal.com/gui/file/44df31da4ce8f4e5a3f9141773d5491f3250de66aa528b6fc2d74ac6adeb2d13
- skid.arm5 – https://www.virustotal.com/gui/file/ab8f295ab1c8c3ce66f8fbda39df4aa8bcbca27d3ddb51b4b18b076c7186a933
- skid.arm6 – https://www.virustotal.com/gui/file/2b1d187f3b6c93569f62b48fc10b627feeffc2f497e1f14965d15b755a2073ae
- skid.arm7 – https://www.virustotal.com/gui/file/15f772d4c6ce512d7442760ae82f2d438bc8496680c950ecef8f56202441912d
- skid.mips – https://www.virustotal.com/gui/file/1b1f226a2de6581606a6aa9249c9d89b9c771a14e02022371405396c278da62d
- skid.mpsl – https://www.virustotal.com/gui/file/4ff0c418b636125fa295ea4467507db85e2ee19c38b1bf921e75fb3f217fae68
- skid.x86 – https://www.virustotal.com/gui/file/859e679f8e8be4a4c895139fb7fb1b177627bbe712e1ed4c316ec85008426db8
The best defense against these attacks and others like them is to replace hardware once it reaches end of life. Barring that, users of EoL devices should at least ensure they’re running the most recent firmware. D-Link provides this dedicated support page for legacy devices for owners to locate the latest available firmware. Another effective protection is to disable UPnP and connections from remote Internet addresses unless they’re absolutely necessary and configured correctly.
Critical takeover vulnerabilities in 92,000 D-Link devices under active exploitation Read More »