Drug cartel hacked FBI official’s phone to track and kill informants, report says
The Sinaloa drug cartel in Mexico hacked the phone of an FBI official investigating kingpin Joaquín “El Chapo” Guzmán as part of a surveillance campaign “to intimidate and/or kill potential sources or cooperating witnesses,” according to a recently published report by the Justice Department.
The report, which cited an “individual connected to the cartel,” said a hacker hired by its top brass “offered a menu of services related to exploiting mobile phones and other electronic devices.” The hired hacker observed “’people of interest’ for the cartel, including the FBI Assistant Legal Attache, and then was able to use the [attache’s] mobile phone number to obtain calls made and received, as well as geolocation data, associated with the [attache’s] phone.”
“According to the FBI, the hacker also used Mexico City’s camera system to follow the [attache] through the city and identify people the [attache] met with,” the heavily redacted report stated. “According to the case agent, the cartel used that information to intimidate and, in some instances, kill potential sources or cooperating witnesses.”
The report didn’t explain what technical means the hacker used.
Existential threat
The report said the 2018 incident was one of many examples of “ubiquitous technical surveillance” threats the FBI has faced in recent decades. UTS, as the term is abbreviated, is defined as the “widespread collection of data and application of analytic methodologies for the purpose of connecting people to things, events, or locations.” The report identified five UTS vectors, including visual and physical, electronic signals, financial, travel, and online.
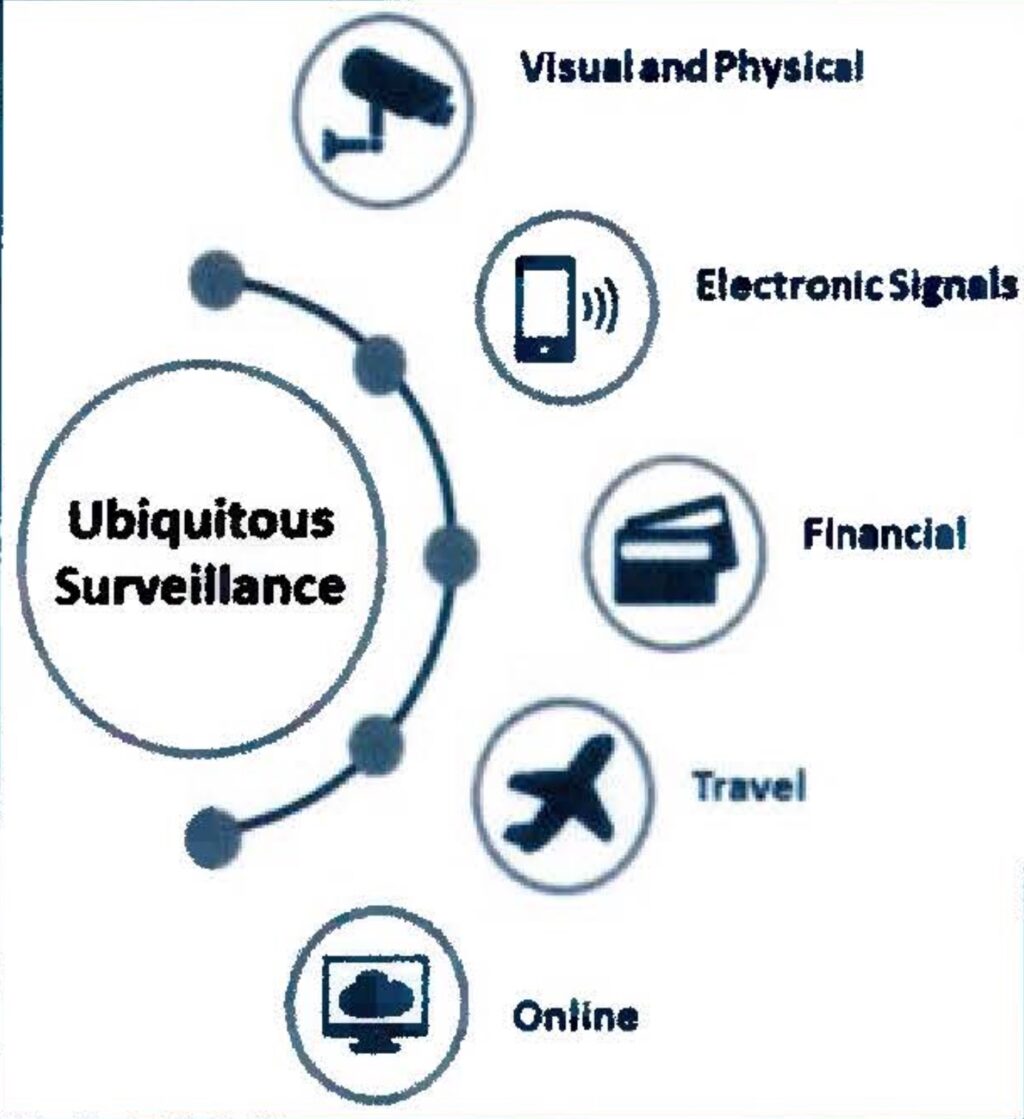
Credit: Justice Department
While the UTS threat has been longstanding, the report authors said, recent advances in commercially available hacking and surveillance tools are making such surveillance easier for less sophisticated nations and criminal enterprises. Sources within the FBI and CIA have called the threat “existential,” the report authors said
A second example of UTS threatening FBI investigations occurred when the leader of an organized crime family suspected an employee of being an informant. In an attempt to confirm the suspicion, the leader searched call logs of the suspected employee’s cell phone for phone numbers that might be connected to law enforcement.
Drug cartel hacked FBI official’s phone to track and kill informants, report says Read More »