From Iran to Ukraine, everyone’s trying to hack security cameras
Research shows apparent Iranian state hackers trying to hijack consumer-grade cameras.
Cameras are placed in public areas in Tehran. Credit: Anadolu/Getty Images
For decades, satellites, drones, and human spotters have all been part of war’s surveillance and reconnaissance tool kit. In an age of cheap, insecure, Internet-connected consumer devices, however, militaries have gained another powerful set of eyes on the ground: every hackable security camera installed outside a home or on a city street, pointed at potential bombing targets.
On Wednesday, Tel Aviv–based security firm Check Point released new research describing hundreds of hacking attempts that targeted consumer-grade security cameras around the Middle East—with many apparently timed to Iran’s recent missile and drone strikes on targets that included Israel, Qatar, and Cyprus. Those camera-hijacking efforts, some of which Check Point has attributed to a hacker group that’s been previously linked to Iranian intelligence, suggest that Iran’s military has tried to use civilian surveillance cameras as a means to spot targets, plan strikes, or assess damage from its attacks as it retaliates for the US and Israeli bombings that have sparked a widening war in the region.
Iran wouldn’t be the first to adopt that camera-hacking surveillance tactic. Earlier this week, the Financial Times reported that the Israeli military had accessed “nearly all” the traffic cameras in Iran’s capital of Tehran and, in partnership with the CIA, used them to target the air strike that killed Ayatollah Ali Khamenei, Iran’s supreme leader. In Ukraine, the country’s officials have warned for years that Russia has hacked consumer surveillance cameras to target strikes and spy on troop movements—while Ukrainian hackers have hijacked Russian cameras to surveil Russian troops and perhaps even to monitor its own attacks.
Exploiting the insecurity of networked civilian cameras is, in other words, becoming part of the standard operating procedures of armed forces around the world: A relatively cheap and accessible means of getting eyes on a target hundreds of thousands of miles away. “Now hacking cameras has become part of the playbook of military activity,” says Sergey Shykevich, who leads threat intelligence research at Check Point. “You get direct visibility without using any expensive military means such as satellites, often with better resolution.”
“For any attacker who is planning military activity, it’s now a straightforward act to try it,” Shykevich adds, “because it’s easy and provides very good value for your effort.”
In the latest example of that recon technique, Check Point found that hackers had attempted to exploit five distinct vulnerabilities in Hikvision and Dahua security cameras that would have allowed their takeover. Shykevich describes dozens of attempts—which Check Point says it blocked—across Bahrain, Cyprus, Kuwait, Lebanon, Qatar, and the United Arab Emirates, as well as hundreds more in Israel itself. Check Point notes it could view attempted intrusions only on networks equipped with its firewall network appliances and that its findings are likely skewed by the company’s relatively larger customer base in Israel.
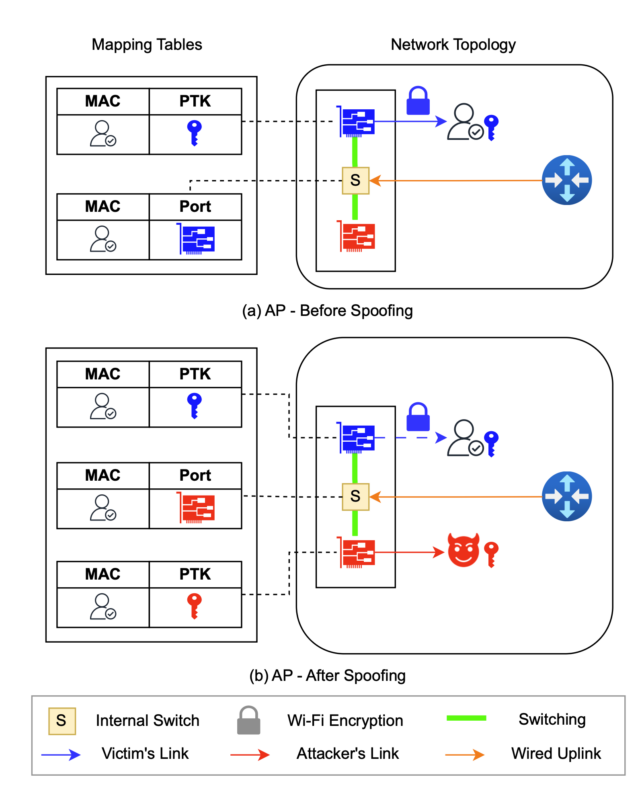
None of the five vulnerabilities are “complicated or sophisticated,” Shykevich says. All of them have been patched in previous software updates from Hikvision and Dahua and were discovered years ago—one as early as 2017. Yet as with hackable bugs in so many Internet-of-things devices, they persist in security cameras because owners rarely install updates or even become aware that they’re available. (Hikvision and Dahua are both effectively banned in the United States due to security concerns; neither company responded to WIRED’s request for comment on the hacking campaign.)
Check Point found that the camera-hacking attempts were largely timed to February 28 and March 1, just as the US and Israel were beginning their air strikes across Iran. Some of the attempted camera takeovers also occurred in mid-January, as protests spread across Iran and the US and Israel made preparations for their attacks. Check Point says it has tied the targeting of the cameras to three distinct groups it believes to be Iranian in origin, based on the servers and VPNs they used to carry out the campaign. Some of those servers, Shykevich notes, have been previously linked in particular to the Iranian hacker group known as Handala, which several cybersecurity companies have identified as working on behalf of Iran’s Ministry of Intelligence and Security.
In fact, Check Point says it tracked similar Iranian targeting of cameras as early as last June during Israel’s previous 12-day war with Iran. The head of Israel’s National Cybersecurity Directorate, Yossi Karadi, also warned at the time that Iranian hackers were using civilian camera systems to target Israelis and had compromised a street camera across from the country’s Weizmann Institute of Science before hitting it with a missile.
The joint US and Israeli strikes on Iran and the assassination of Khamenei have revealed, however, just how thoroughly Israel’s own hackers—or those of its allies, including potentially the US—had penetrated Tehran’s camera systems, too. Israeli intelligence sources speaking to the Financial Times described assembling the patterns of life of Iranian security guards around Khamenei based on the real-time data that traffic cameras provided across the city. “We knew Tehran like we know Jerusalem,” one source told the FT.
Prior to the current escalating war in the Middle East, the powerful surveillance role of hacked civilian cameras first became apparent in the midst of Russia’s war in Ukraine. Ukrainian officials warned in January 2024, for instance, that Russian forces had hacked two security cameras in the capital of Kyiv to observe Ukrainian infrastructure targets and air defenses. “The aggressor used these cameras to collect data to prepare and adjust strikes on Kyiv,” reads a post from Ukraine’s SSU intelligence service.
The SSU went so far, it writes, as to somehow disable 10,000 Internet-connected cameras—it didn’t reveal how—that could be used by Russia’s military. “The SSU is calling on the owners of street webcams to stop online broadcasts from their devices, and on citizens to report any streams from such cameras,” the post reads.
Even as Ukraine has attempted to block that spying technique, it seems also to have adopted it. When the Ukrainian military used its own underwater drone to blow up a Russian submarine in the bay of Sevastopol in Crimea, it published video that defense-focused news outlet The Military Times noted looked very much like it had come from a hacked surveillance camera. A BBC report about Ukrainian hacktivist group One Fist notes more explicitly that they were commended by the Ukrainian government for work that included hacking cameras to watch Russia’s movement of matériel across the Kerch Bridge between Russia and Crimea.
“The advantages of co-opting a civilian camera network are presence and expense,” says Peter W. Singer, a military-focused researcher at the New America Foundation and the author of the 2015 science fiction novel Ghost Fleet, which imagines future war scenarios. “The adversary’s already done the work for you. They’ve placed cameras all around a city.”
Singer notes that hacking those cameras is vastly cheaper and easier than relying on satellites or high-altitude drones. The trick is stealthier than drones, too, which are only viable when the enemy has few air defenses, and drones can often be detected by countersurveillance measures. Ground-level, hacked cameras also offer angles and perspectives that aren’t possible with the bird’s-eye view of a satellite or drone, he adds. All of that makes them powerful tools for reconnaissance, targeting, and what he calls “bomb damage assessment” after a strike.
Hacked cameras are a tough problem to solve, in part, because those who have the ability to secure them rarely suffer the consequences of that surveillance, says Beau Woods, a security researcher who formerly worked as an adviser to the US Cybersecurity and Infrastructure Security Agency. “The manufacturer of the device and the owner of the device are not the victim,” Woods says. “So the victim isn’t in a position to control the tool that’s used by the adversary.”
The difficulty of pinning down responsibility for Internet-connected consumer cameras means that their role in military surveillance is likely to persist for many years—and wars—to come.
“Who’s liable, who’s responsible, who’s accountable?” Woods asks. “The camera itself is not directly causing the harm. But it’s part of the kill chain.”
This story originally appeared on wired.com.
From Iran to Ukraine, everyone’s trying to hack security cameras Read More »