The 2025 Aston Martin Vantage: Achingly beautiful and thrilling to drive
The new infotainment human-machine interface was a little confusing at first; pairing my phone took about 10 minutes but worked out in the end, and wireless Apple CarPlay behaved itself throughout the week. When starting the car there was sometimes a lengthy wait for the infotainment to boot up, as if the hardware wasn’t quite powerful enough for the software stack on top.
Don’t get it wet?
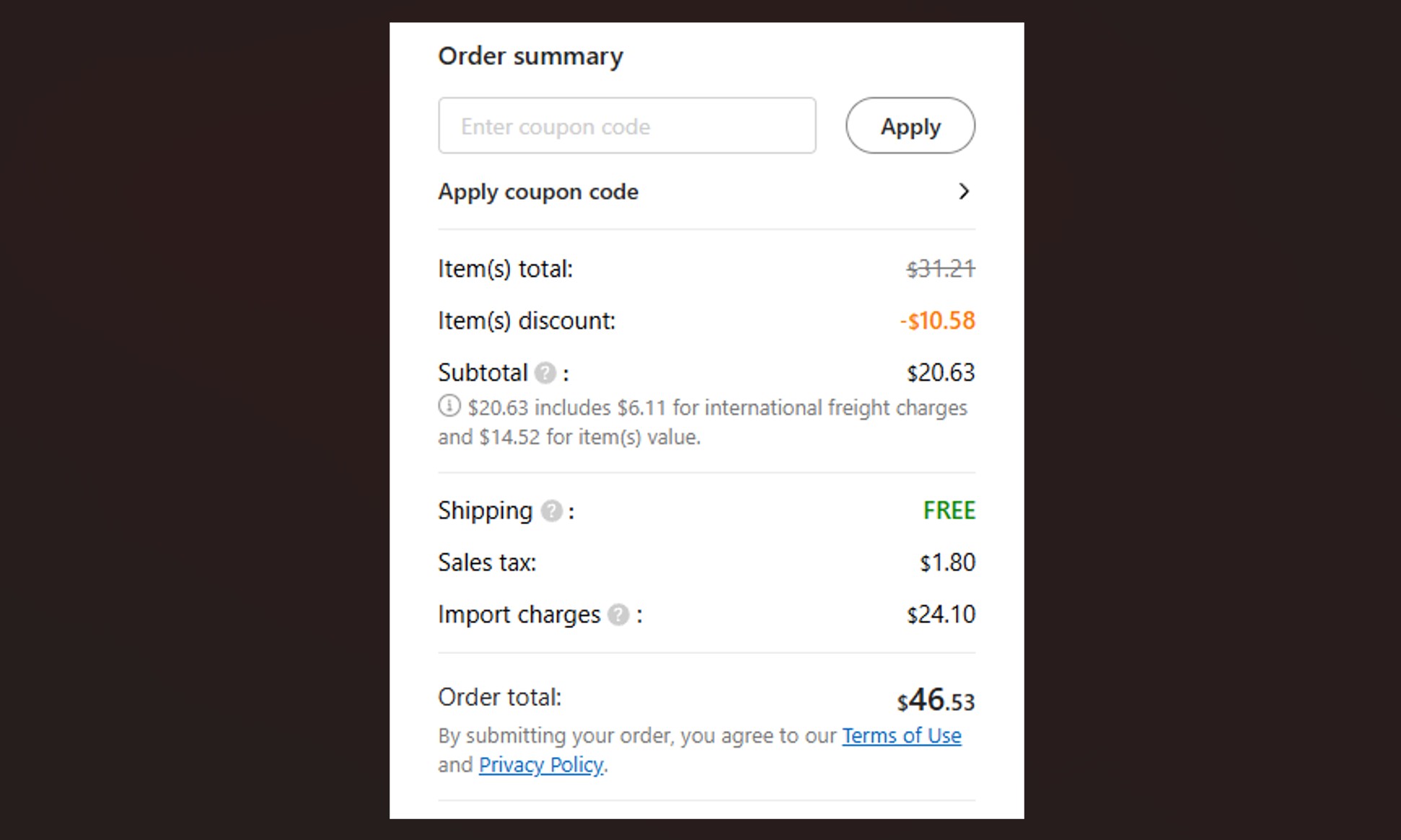
Those are very minor complaints compared to what happened when it rained really hard, though. I had been planning to drive the Vantage to dinner, but upon getting in the car and turning it on, I realized it had other ideas. A number of yellow glyphs remained brightly illuminated on the digital main display—including traction control. A series of notifications informed me of what else wasn’t working, including the ability to switch the car into Wet mode.
Inclement weather. Jonathan Gitlin
With the numbers “$264,300” and “656 hp” at the forefront of my mind, the DC metro sufficed for that trip.
Later that evening, the air still damp but no longer raining, it was if it had all been a dream. A push of the start button and everything lit up and then went dim as normal. The infotainment even booted in an acceptable time. My guess is that there was an improperly sealed connector somewhere, and in torrential rain, water got where it shouldn’t. Regardless, the car let me down when it was supposed to take me somewhere.
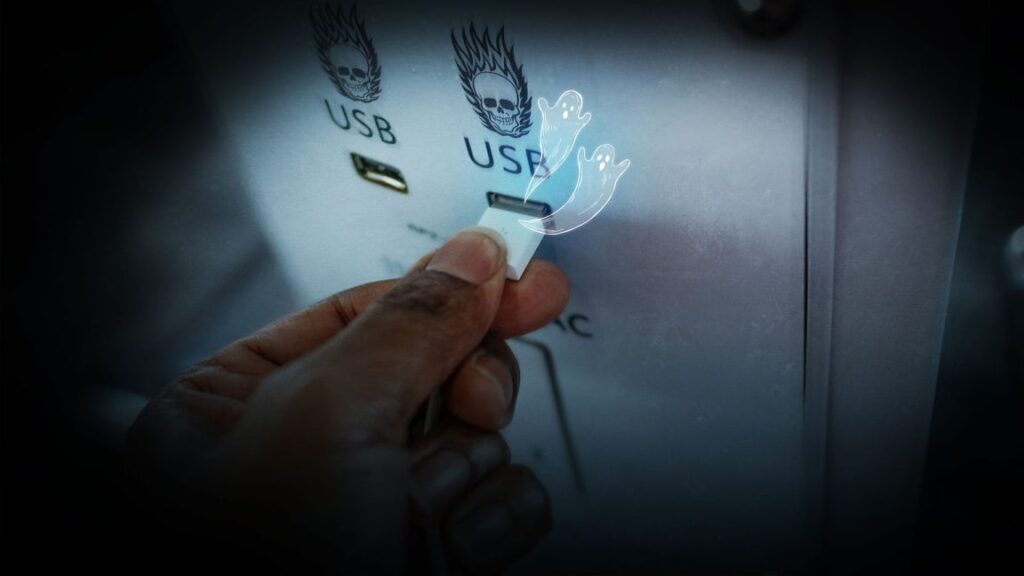
As a former resident of the UK, it saddens me to no end that the stereotype about British cars and their electronics is as true today as ever, but the fact remains that every British car I drive, from Minis to McLarens, manages to have some kind of digital or electrical foible that should have been ironed out. Do better, Britain!
With a base price of $191,000, the Vantage is competing with a number of other sports cars, but its biggest rival has to be the Porsche 911 Turbo. It’s a much more dramatic car than the Porsche, in all the meanings of that word, both good and bad.

Credit: Jonathan Gitlin
Sure looks good though.
The 2025 Aston Martin Vantage: Achingly beautiful and thrilling to drive Read More »